
Our Managed Security Operations Center (SOC) focuses on complete coverage for your business with real-time threat hunting and monitoring.
Business Value
Fortify Your Team's Cybersecurity
Cyber Threats Have Nowhere to Hide
Cyber threats hide in your system for an industry average of 200 days. Catch them immediately with Blue Sentinel.
Not Just a Tool,
It's a Team
Our Managed Detection & Response service leverages best in class tools, but the real value-add is the 24/7 support from our Managed Security Operations Center analysts.
Grow Revenues and Reduce Cost
Offload the burden of security monitoring from your IT team so that they can focus on delivering new technology and efficiencies to your business.
Let Us Free Up Your SOC Resources
Blue Sentinel’s Managed Detection and Response (MDR) service puts our in-house experts at your fingertips to act quickly on every threat that puts your network and reputation at risk, so you can focus on what you’re best at and keep your resources where they’re most effective.
The Most Reliable Managed SOC
Our Managed Security Operations Center (SOC) can take the burden of cybersecurity off the shoulders of your IT team.
24/7 Coverage
Our security analysts monitor your environment around the clock to proactively hunt threats and provide complete coverage.
Lightning Fast Detection & Response
Our SOC substantially reduces detection and response time. Most threats take upwards of 200 days to detect, but we can respond within minutes.
Peace of Mind
Our SOC allows your business to offload the burden of threat monitoring so that it can focus on the day-to-day operations of the business.
Visibility
Our SOC simplifies and contextualizes your alerts in a centralized, easy-to-use dashboard to provide a clear window into your environment.
Clear Reporting
Our analysts provide frequent and detailed reports with actionable items to remediate any security gaps within your environment.
Customized Service
As an extension of your team, our priority is to provide complete security coverage that fits your business’s specific needs.
Ready to Take a Look?
Experience cybersecurity that prevents threats at faster speed, greater scale, and higher accuracy.
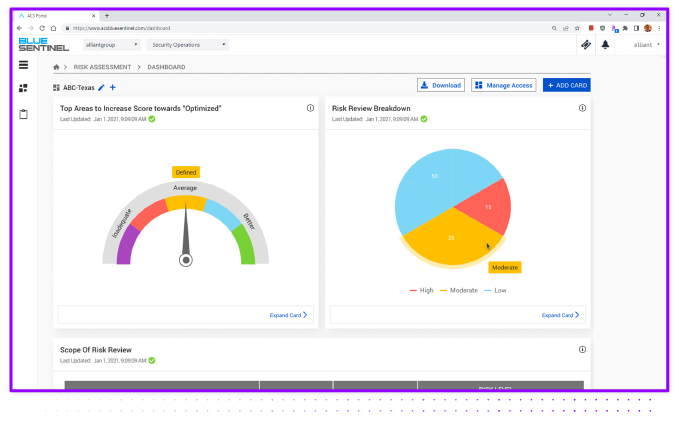
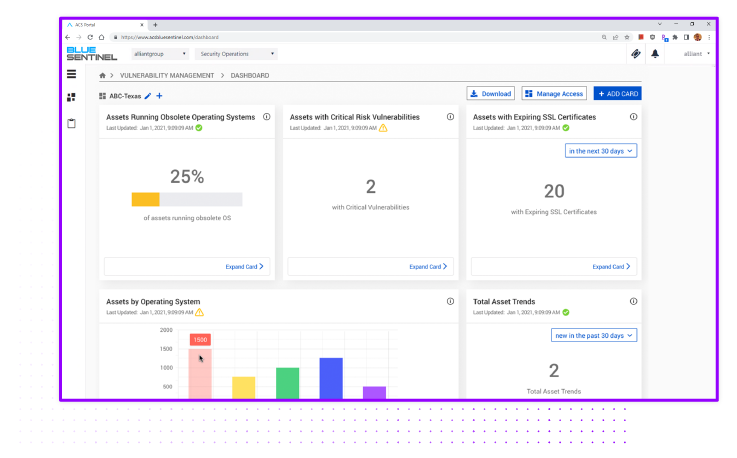
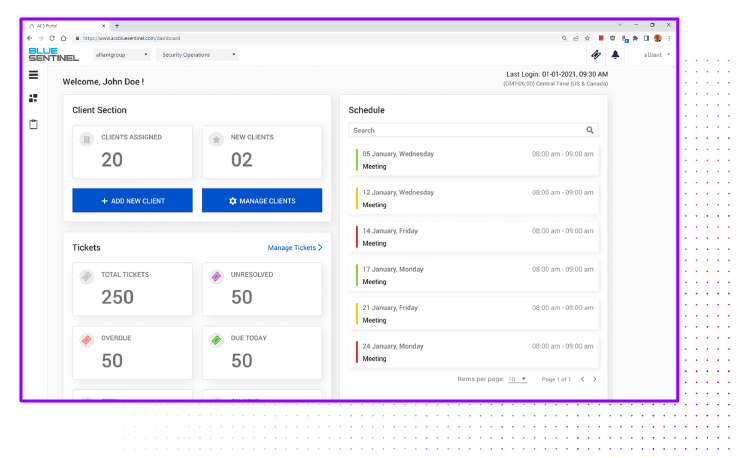
Constant Vigilance, Rapid Response, & Dashboard Visualization
In addition to the team of dedicated cybersecurity engineers, Managed SOC delivers a range of visualization options, from dashboards to customized reports. These deliverables and on-going reports are built for you, providing the information you need to be in control of your cyber posture at all times.
Our dashboards constantly monitor the cybersecurity threat landscape for your business, and present it in a clear and concise manner, allowing you to efficiently notice. Understand, and act on your business’ security situation.
Presenting the Managed SOC in interactive dashboards allows your business to isolate weaknesses faster and more efficiently identify the needs and shortcomings of your current cybersecurity tools. Furthermore, presenting the vulnerabilities this way more effectively highlights the necessary steps your business needs to take to remain safe.
Effective
Isolate weakness and potentially identify the short comings of your current cyber tools and software
Readable
Maximize visibility of all threats and vulnerabilities across every corner of your enterprise
Comprehensive
Constantly monitor the cybersecurity threat landscape for your business and see it all in one place
SOC as an Alliant Cybersecurity Service
Managed Security Operations Center
People
Global Team of security analysts and experts proactively hunt, analyze and remediate threats around the clock
Process
Scoring and triaging system provide deep contextualization and correlation across all the endpoints, devices and apps
Technology
SIEM and MDR tools detect, triage and provide remediation process before a breach can occur
SIEM
MDR
VCISO
- Correlation Engine
- Threat Intelligence
- User and Entity Behavior Analytics (UEBA)
- Malware Detection
- Kill Chain Analysis
- Threat Hunting
- Incident Response
Offload
Compliance and Security related questions, Cybersecurity Concerns, Logs from End points, Devices, apps (on-prem, SaaS), and Cloud Platforms
Alerting and Reporting
Alerting on anomalies and vulnerabilities, Security Strategy Advice, Incident Management, and Periodic Reports
Completely Customized Service
Businesses are now more aware than ever of the impact a cyber attack can have, from extortion and production downtime to reputational damage and potential litigation. Yet, the steps to address threats are often seen as an IT cost rather than a cost of doing business.
Managed SOC takes cybersecurity off your plate, by being your in-house defense and response team at a fraction of the cost of assembling your own team. If we see an event, behavior, or any suspicious activity, our security operations center will respond immediately to protect your business and people. A cybersecurity strategy that has data-driven threat intelligence and built-in analytics is critical, and that’s where Managed SOC delivers.

Dedicated Cybersecurity Engineers
Blue Sentinel, with its team of dedicated cybersecurity engineers provides a complete cyber service with the flexibility to scale to your needs and customized solutions to ensure you have a 24/7/365 coverage service that is built for you.
Through vulnerability assessments and proactive threat hunting, our security engineers actively look for evidence of a cyber-attack or event, collecting threat intelligence from open source intelligence and industry renowned threat intelligence feeds, identifying key indicators of compromise, and using our teams to respond to identified threats.
