With just one more week to go in Cybersecurity Awareness Month, let’s recap the ground we’ve covered in the first three of five installments before moving on to Phase 4, Compliance.
- Start your journey with a risk assessment. Taking stock of your Strengths, Weaknesses, Opportunities, and Threats from a holistic viewpoint of People, Process, and Technology using a recognized framework should help determine your risk appetite and give you that vital roadmap to start improving.
- Incorporate Data Privacy and Cybersecurity controls into your organization. Start at the beginning of each major project and aspect of the business rather than hurriedly bolting them on as an afterthought. It is less expensive, and the controls will generally be less invasive and still more effective. A knowledgeable and experienced Security Architect is a must for this phase.
- Effective operational implementation and metrics of the controls around Data Privacy and Cybersecurity are the means by which organizations improve their risk management posture. These are each key elements:
- Education and Awareness Training,
- Policy Planning,
- Vulnerability Management,
- Penetration Testing,
- Thought Leadership,
- Services Provider Partnerships, and
- Metrics
Security and compliance are related but not the same. By that, I mean, it is possible to be compliant but not secure enough, and vice versa. Compliance is about adequately meeting stated governance and control requirements from an external entity. At an organizational level, it is achieved through management processes which identify the applicable requirements (defined for example, in codified statutes, regulations, and contracts), assess the state of current compliance, assess the risks and potential costs of non-compliance against the projected expenses to achieve compliance, and hence prioritize, fund and initiate any corrective actions deemed necessary. Examples include but are not limited to:
- If you take credit cards for payment, you must be Payment Card Industry – Data Security Standard (PCI-DSS) compliant
- If you do business with European Union residents, you must be General Data Protection Regulation (GDPR) compliant
- If you are a financial institution, you must be Gramm–Leach–Bliley Act (GLBA) compliant
- If you work with Protected Health Information (PHI), you must be Health Insurance Portability and Accountability Act (HIPAA) compliant
- If you are part of the US Government supply chain, you will soon likely have to be Cybersecurity Maturity Model Certification (CMMC) compliant
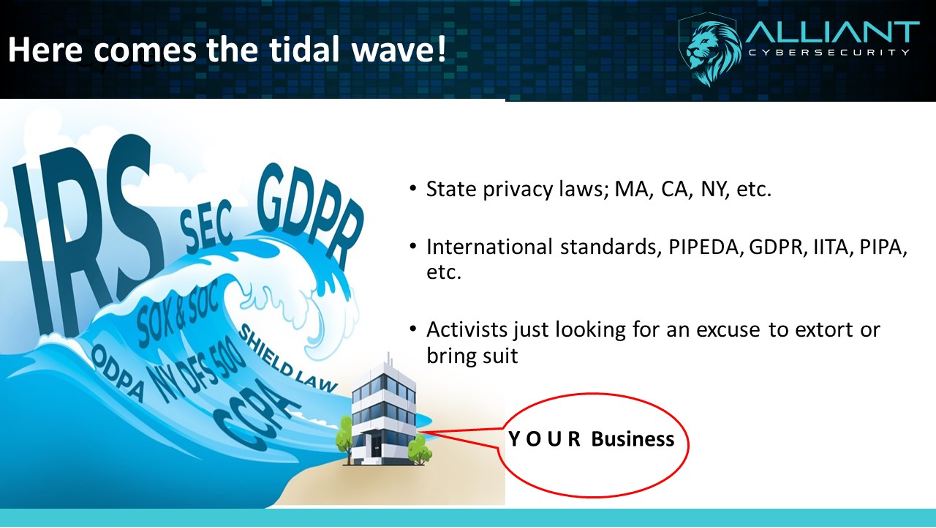
Additionally, for various industries, US states (e.g., CA, NY, MA, etc.), and types of transactions, the list of compliance required goes on and on. There is no single world or USA-wide standard as of yet, but the tsunami of regulations and requirements is intended to force two outcomes. The first is better cybersecurity hygiene, and the second is to protect what are now seen as the inherent rights of individuals with regard to their personal information. This new emphasis also carries an expansion of what constitutes personal information. Things like someone’s image, cookie file collections from their devices, political preferences, and other previously somewhat innocuous data points are now considered personal information. These newly recognized rights about personal information include:
- The right to be informed of personal information being collected
- The right of access to that personal information by the data subject
- The right to correct errors in that collected information
- The right to object to processing
- The rights in relation to automated decision making and profiling based on the information collected
- The right to be forgotten (the right to erasure)
- The right to data portability
- The right to restrict processing
The bad news is two-fold. Organizational size is not normally much of a factor in whether you must comply or not. The second is that this compliance means added expense to most organizations. The good news is also two-fold. According to a 2019 survey conducted by Cisco, companies investing in compliance programs are seeing benefits like operational efficiency and agility. Also, nearly half of those organizations surveyed reported benefits valued at least 2X the spend on compliance!
So how do you get compliant? It starts with determining which regulations or standards are currently applicable or likely will be in the near future for your organization. The second step is a thorough and objective compliance readiness assessment that determines where you are presently and what gaps exist that must be bridged before your organization can become compliant. The third step is remediation, fixing the shortcomings. In some cases, after all the remediation is complete, the last step is an actual audit or certification by an external qualified certifying entity.
A programmatic approach is the best way to achieve this end. Many organizations just do not have the skill sets, knowledge, or experience to accomplish this goal. Hiring a qualified FTE individual to spearhead creating, implementing, and monitoring the program is often cost-prohibitive. In addition to mapping all the types of personal information your organization collects, where it is stored, how it is shared/sold, how it is used, and how long it is retained, there is a great deal of written policy work involved with becoming compliant. That is where a trusted advisor partner like Alliant Cybersecurity can add value in short order. Already knowing where the rocks are in the stream and having pragmatic means of assessing and then helping to implement controls to meet the requirements can save countless work hours.
Some organizations will contend they have no compliance issues since they are business to business (B2B) vs. business to consumer (B2C). That could be true in some cases. However, that probably won’t stop the zealous compliance activists from coming after you in court. For instance, the California Consumer Privacy Act (CCPA) only became effective in January 2020. Nonetheless, there are already hundreds of lawsuits on the docket, most as class actions and at least 50 are against B2B companies headquartered outside the state of California! Legal experts advise that every organization should at least formally assess their current state of compliance and then base their decision on what compliance steps should be taken to embrace the new normal given the litigious nature of the world today.
In summary, organizations should determine what compliance requirements may encumber them and formally decide on the next steps, which could include a compliance readiness assessment, remediation, and formal implementation of a compliance program. The controls need to be tailored for your organization, sustainable, and scalable. Metrics that clearly communicate the good and the bad aspects of your ongoing program are a must.
Our fifth and last installment will address how to prepare for and then mount an effective response to an inevitable cybersecurity or data privacy event. As a hint, it is a much bigger and a potential organization upending issue than just calling your IT Department or Managed Services Provider. Thank you for your time and call on us if we can help. In the meantime, BE AWARE. BE SECURE.



