Bad actors online love to prey on tragedy and fear to make a profit. Unfortunately, it seems as though coronavirus is no exception, and there are phishing emails circulating designed to capitalize on the worldwide pandemic. With the world in a panic, everyone should be even more vigilant when it comes to cybersecurity than ever.
Did the CDC Send me an E-mail?
Phishing scams are the most successful type of cyber attack on small and medium sized businesses. Their success lies in their simplicity. A hacker does not need to use complex code or repel from the ceiling into your server room to access sensitive data at your company. All an attacker needs to do, in this case, is get an employee to click on a link.
It does not take much more than that for a hacker to infect your network, gain access to your data, or even lock your entire business out of your systems until a ransom is paid. For bad actors, the trick is to make you and your employees believe that the message you received is legitimate. Usually, attackers will pose as a figure within your organization or a governmental authority figure. They will then create a sense of urgency to elicit an action that will expose the recipient.
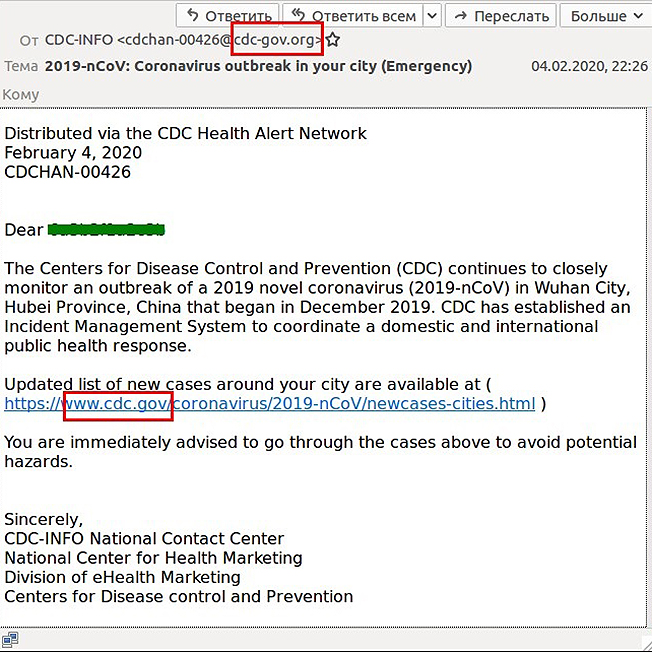
Cybercriminals are now posing as representatives of the Centers for Disease Control and Prevention (CDC) to get people to click on a malicious link. The e-mail claims to be offering information about coronavirus infections in the recipient’s area if they follow a link. It is estimated that 3% of domains online related to coronavirus are malicious.
The problem is so widespread that government officials in several states are issuing warnings to staffers to be on heightened alert for phishing scams. The U.S. Department of Homeland Security has also issued an alert to be vigilant about coronavirus phishing scams.
There is also an ongoing phishing campaign where attackers send emails that appear as though they are from the World Health Organization (WHO). The message asks people to click a malicious link that claims to provide safety measures on coronavirus. The WHO has gone so far as to establish a page with tips for avoiding corona related phishing scams and a page to report suspected scams.
How to Know if an Email is a Phishing Scam
It is necessary to train your entire organization on the dangers of phishing emails as it only takes one person to infect your entire network. Here are some things to look out for to avoid phishing attacks.
- Check the Sender Address – The first big giveaway that a message may be a phishing scam is the sender address. Phishing emails usually send from an address that may look legitimate but is just slightly off. Check and make sure the e-mail domain matches the website domain of the government entity. For instance in the phishing email to the right, the message comes from a .org domain but the CDC website is a .gov domain.
- Check the Link but DON’T Click It – If you are wary of a link in an e-mail, which you always should be, you can try mousing over the link to see if it reveals an alternative link address. While the link text may say “.gov,” hovering over the link may reveal a different address all together.
- Provide No Information – Many times phishing emails will not have a link but may simply ask that you provide sensitive data or passwords. If you are suspicious and the email is requesting personal data, do not reply.
- Do Not Give in to Pressure – Hackers will use fear and urgency to trick people into making a mistake. With coronavirus, hackers are banking on people’s fear but they may also use threats of prosecution to try to force your hand.
- Check Typos, Grammar, Phrasing – You would be surprised just how un-sophisticated some of these attackers may be. Many phishing emails are littered with typos and grammatical errors. Hackers send phishing attacks from all over the world and their English is often barely passable. If there is odd phrasing or terminology, that should be a red flag as well.
Again, it is important that you and your staff are all trained on how to spot a phishing email. Organizational training is a crucial component of any cybersecurity plan. If you are at all uncertain about your cybersecurity framework, reach out to Alliant Cybersecurity for a complimentary Impact Assessment.



